
A secure supply chain is the set of governance practices, controls, and verification mechanisms that ensure hardware, software, services, data, and suppliers are authentic, trustworthy and resilient, and free from compromise. It encompasses the full lifecycle of a supply chain — from sourcing and procurement, to development, integration, distribution, maintenance, and end‑of‑life.
At its core, secure supply chain aims to answer three critical questions:
- Do we know what is in our supply chain?
- Can we trust every component and supplier involved?
- Can we detect, prevent, and respond to risks across all tiers of the ecosystem?
It is both a cybersecurity discipline and an operational resilience practice, bridging procurement, risk, IT, engineering, and compliance into a unified security function.
If you’re defining your organisation’s posture – or need to lift maturity without slowing delivery – we can help.
Types of Secure Supply Chain
Modern secure supply chain can be understood through three overarching domains. Each represents a different set of risks, controls, and assurance practices that organisations must manage to protect the integrity of their hardware, software, data, and suppliers.
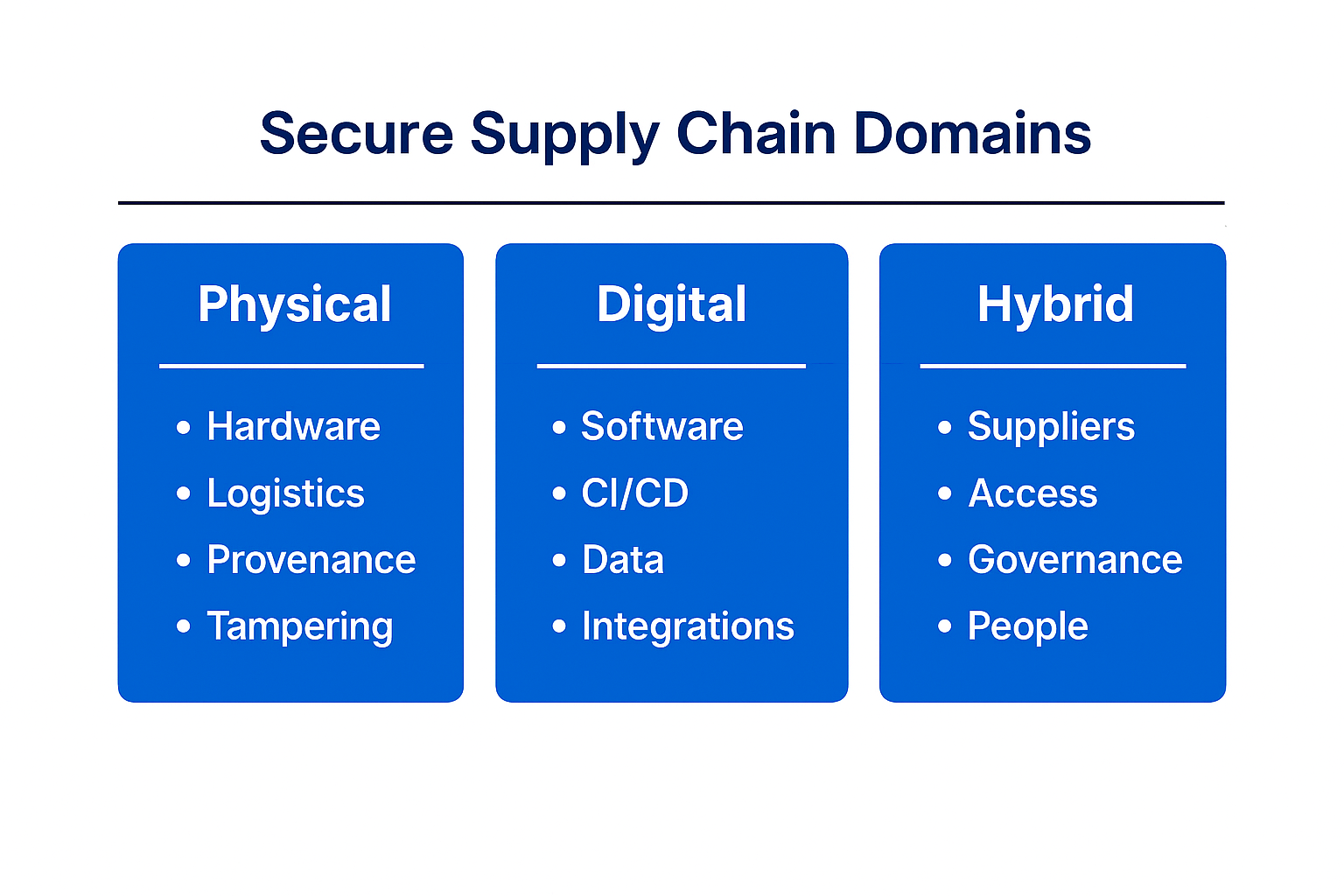
Physical Supply Chain Security
Physical supply chain security protects the tangible components, logistics pathways, and movement of hardware from manufacturing through to final delivery. It focuses on ensuring products are authentic, untampered, and securely transported. Key measures include:
- Hardware authenticity & provenance
- Country-of-origin assurance
- Secure logistics & transportation
- Tamper-evident sealing
- Chain-of-custody controls
- Protection against counterfeit components
- Warehouse security & controlled storage
Digital Supply Chain Security
Digital supply chain security protects the software, data, and code dependencies that flow between organisations. It addresses threats that enter through updates, integrations, cloud services, data exchanges, or development pipelines. Key components include:
- Software supply chain security
- CI/CD pipeline and build system security
- Software bill of materials
- API and integration security
- Data protection
- Data visibility, governance & sharing controls
- Cloud & platform service assurance
- Identity and access for third-party systems
Hybrid Security
Hybrid supply chain security covers the people, processes, and multi-tier supplier relationships that sit between physical and digital systems. It addresses risks introduced by vendors, partners, contractors, and operational workflows. Key measures include:
- Vendor and third-party management
- Multi-tier supplier assurance
- Secure procurement and onboarding processes
- Fraud prevention across transactions
- Data locality and regulatory compliance across jurisdictions
- Operational governance and access controls
- Service provider oversight
By mapping secure supply chain measures into three overarching types (physical, digital, and hybrid), businesses can organise their approach around the full lifecycle of risk. Together, these domains form a complete and modern framework for understanding secure supply chain challenges.
Why Secure Supply Chain Matters
The role of supply chain security has evolved rapidly. What was once an operational consideration buried in procurement and vendor management has become a strategic priority for boards, regulators, and customers. Organisations now operate in an environment where trust, continuity, and transparency are decisive competitive factors – and each one is shaped by the strength of the supply chain behind them.
Modern businesses rely on a vast ecosystem of third‑party technologies, logistics networks, and service providers. This interconnectedness creates opportunity, but it also means that an organisation’s resilience is directly tied to the security practices of every partner it works with.
- Threats Are No Longer Confined to the Organisation Itself
Attackers increasingly exploit suppliers, service providers, and software components as steppingstones. This shift means organisations must think beyond their internal perimeter and recognise that supplier integrity is now a critical part of their defensive posture.
- Third‑Party Dependency Is Now Fundamental to Digital Operations
Cloud‑first strategies, outsourced functions, and complex software stacks mean that core business systems operate across environments organisations don’t fully control. Ensuring those external environments are secure is now essential to protecting internal operations.
- Trust and Transparency Shape Buyer Decisions
Customers, particularly in regulated or high‑assurance industries, want visibility into how products are sourced, built, and maintained. The ability to demonstrate supplier assurance and produce evidence of secure practices has become a differentiator in procurement processes.
- Regulatory Standards Are Elevating Expectations
Around the world, governments and industry bodies are introducing stricter requirements around supplier assurance, secure procurement, and risk management. Securing the supply chain is no longer just practical – it is increasingly mandated.
- Business Continuity Relies on Supply Chain Stability
Disruptions in manufacturing, logistics, or upstream technology can halt operations entirely. Secure supply chain practices reduce the risks of outages, tampering, or compromised components, reinforcing overall operational resilience. - Security Maturity Enhances Competitive Positioning
Organisations that invest in supply chain security are better positioned to win enterprise deals, reduce incident-related costs, and build long‑term trust. Strong security is moving from cost centre to value driver.
Key Challenges to Secure Supply Chain
While the strategic importance of supply chain security is clear, the path to delivering it is not straightforward. Organisations face structural, operational, and environmental challenges that make supply chain assurance complex and resource‑intensive. These are the key barriers shaping the landscape today.
- Limited Visibility Across Multi‑Layered Supply Networks
Most organisations can assess direct suppliers, but deeper tiers – subcontractors, software dependencies, open‑source libraries, or offshore manufacturing partners – remain opaque. This lack of visibility creates blind spots where vulnerabilities can hide.
- Suppliers Vary Widely in Security Maturity
Vendors differ significantly in their processes, capabilities, and willingness to provide assurance. Smaller providers may lack resources to implement robust controls, while larger ones may be slow or constrained in what evidence they can share. This inconsistency makes standardised assurance difficult.
- Compliance and Due‑Diligence Burdens Are Growing
As regulations expand, organisations face more documentation requirements, audits, and scrutiny across procurement and operations. Aligning multiple suppliers to meet these evolving standards creates friction, especially when dealing with legacy vendors or global supply routes.
- External Disruption Creates Operational Uncertainty
Geopolitical tension, supply shortages, manufacturing bottlenecks, and shifting trade policies introduce instability. These disruptions can affect the availability, integrity, or provenance of components, making secure sourcing more challenging to maintain.
Best Practices for Supply Chain Security
Securing the supply chain requires a combination of modern security models, strong governance, and continuous verification. These practices help organisations reduce exposure, improve resilience, and protect the integrity of every product, service, and dependency they rely on.
- Apply Zero Trust Principles Across the Supply Chain
Zero Trust assumes no supplier, system, or component is trustworthy without verification. Every interaction must be authenticated, authorised, and monitored.
In practice, this means extending Zero Trust beyond internal networks to suppliers and service providers, aligning with frameworks such as NIST Zero Trust Architecture and NIST SP 800‑161 (C‑SCRM). By continuously validating identities, access, and integrity across organisational boundaries, organisations limit how far an attacker or compromised supplier can move through the ecosystem.
2. Strengthen Software Integrity
Modern supply chains depend heavily on open‑source code, third‑party libraries, SaaS platforms, and automated build pipelines — all of which can be exploited. Strengthening software integrity requires adopting recognised software assurance models, including
- Secure Software Development Frameworks (e.g. NIST SSDF)
- Software Bills of Materials (SBOMs) for component transparency
- Build and provenance controls (e.g. signed artefacts, hardened CI/CD environments)
These practices ensure organisations can prove what is in their software, how it was built, and whether it has been altered — a requirement increasingly embedded in government and critical‑industry procurement.
3. Govern Third-Party Risk Continuously
Supplier risk is not static. Vendors change ownership, adopt new platforms, subcontract services, or experience security incidents that materially alter their risk profile.
Effective supply chain security requires continuous third‑party risk governance, not point‑in‑time assessments. This aligns with:
- ISO/IEC 27036 (supplier relationship and supply chain security)
- ISO/IEC 27001 supplier controls
- NIST SP 800‑161 enterprise‑level C‑SCRM programmes
Continuous governance includes ongoing assessments, contractual security obligations, evidence‑based assurance, and posture monitoring to ensure suppliers maintain required standards over time.
4. Protect Physical Hardware and Logistics
Securing the physical supply chain is as critical as securing the digital one — particularly for ICT, OT, defence, and critical infrastructure environments.
Best practice includes validating country of origin, preventing counterfeit components, enforcing tamper‑evident packaging, using trusted logistics providers, and maintaining formal chain‑of‑custody documentation. These measures align with ISO 28000 and, in Australian government and defence contexts, with ACSC ISM and PSPF requirements.
5. Monitor Constantly and Prepare to Respond
Supply chain threats can emerge without warning — through supplier breaches, compromised updates, logistics interference, or geopolitical disruption.
Organisations should continuously monitor supplier incidents, track emerging vulnerabilities, integrate threat intelligence, and maintain shared incident response and notification arrangements with critical vendors. Coordinated response planning ensures incidents are contained quickly and accountability is clear.
This approach aligns with modern resilience expectations embedded across NIST, ISO, and government protective security frameworks.
Benefits of Strengthening Supply Chain Security
A robust supply chain programme delivers significant advantages over basic threat prevention:
- Greater Protection Against Modern Threats
A stronger supply chain security posture reduces exposure to the fastest‑growing attack vectors, including compromised suppliers, poisoned updates, and tampered hardware. By validating every component and partner before it enters your environment, organisations dramatically lower the risk of breaches that spread through trusted channels.
- Improved Operational Resilience
Resilient supply chains experience fewer disruptions, whether caused by cyber incidents, hardware tampering, or weaknesses in lower‑tier vendors. Strengthening security ensures that products, updates, and services arrive intact and on time, enabling organisations to maintain critical operations even when external conditions become unpredictable.
- Increased Visibility and Control Across the Ecosystem
Enhancing supply chain security provides clearer insight into how software, hardware, and data move through multiple partners and tiers. With better transparency comes better decision‑making — organisations can identify vulnerabilities earlier, respond faster to emerging issues, and maintain consistent control over their extended environment. - Stronger Trust with Customers, Regulators, and Stakeholders
Customers and regulators expect evidence‑based assurance that organisations can protect their upstream and downstream dependencies. By demonstrating mature supply chain security practices, businesses earn trust, strengthen their reputation, and meet rising compliance expectations across industries such as defence, financial services, and critical infrastructure. - Competitive Advantage and Long‑Term Cost Reduction
Organisations with secure supply chains move faster through procurement, face fewer remediation costs, and avoid the reputational damage associated with supply chain‑driven incidents. Strengthening supply chain security reduces the likelihood of costly breaches and disruptions, while positioning the business as a reliable, high‑assurance partner in the market.
Trends Shaping Secure Supply Chain
- Rapid Adoption of AI and Automation
AI is becoming embedded across forecasting, logistics, and supplier management, enabling faster decisions and more precise risk detection. As automation expands, supply chains gain speed and intelligence — but also increased dependency on digital systems.
2. Demand for Real-time Visibility and Transparency
Organisations are moving from periodic reporting to continuous visibility, using real‑time data to understand supply status, shipment movement, and upstream vulnerabilities.
3. Increased Use of Digital Twins for Risk Simulation
Digital twins allow organisations to model their entire supply chain environment, simulate disruptions, and identify weak points before they manifest in reality.
4. Growing Focus on Sustainable and Ethical Supply Chains
Sustainability and responsible sourcing are becoming core requirements, driving demand for greater transparency across supplier networks. This shift naturally reinforces the need for secure data, clear provenance, and stronger oversight across all tiers.
5. Rising Demand for Digital and Risk-Focused Skills
As supply chains become more technology‑driven, organisations need teams with stronger digital, analytical and security capabilities. This trend is pushing supply chain, procurement, and cyber teams to collaborate more closely and develop new competencies.
6. Shift Toward Resilient, Multi-Sourced Networks
Efficiency‑only supply chains are being replaced by models built for resilience. Organisations are diversifying suppliers, reducing single points of failure, and redesigning networks to better withstand disruptions — including cyber incidents, geopolitical shifts, and physical interruptions.
Key Considerations and Decision Factors
- Identify What’s Most Critical to Protect
Organisations need a clear view of which suppliers, components, and data flows are mission‑critical. High‑impact systems require stronger controls and more frequent assurance, while lower‑risk areas can follow lighter processes. Understanding criticality ensures security investments are targeted, not scattered.
2. Evaluate Supplier Transparency and Multi-Tier Visbility
Not all suppliers offer the same level of security maturity or openness. Decision‑makers must consider how much visibility they have into a supplier’s practices — and their downstream dependencies. Suppliers that provide clear, verifiable information and cooperate during incidents are far lower risk than those operating in opacity.
3. Balance Security with Compliance and Long-Term Sustainability
Supply chain security must align with regulatory obligations, operational capacity, and future growth. Controls should be strong enough to withstand evolving threats but practical enough to maintain over time. The right decisions balance compliance, risk reduction, and the ability to sustain secure practices at scale.
How Touchpoint Helps Strengthen Your Secure Supply Chain Efforts
Touchpoint enhances secure supply chain resilience by protecting the physical movement, integrity, and provenance of ICT hardware throughout its lifecycle. Through measures such as tamper‑evident sealing, Defence‑approved secure logistics, obfuscated recipient information, non‑descriptive packaging, and formal chain‑of‑custody documentation, Touchpoint ensures that equipment arrives authentic, uncompromised, and aligned with ISM requirements.
We also support trusted hardware sourcing, including TAA‑compliant and approved‑origin products, and provide controlled shipping manifests only after delivery to safeguard sensitive routing information. These layered controls create a robust, end‑to‑end physical security model that reduces interference risks and reinforces the integrity of mission‑critical systems.
Find out more about our secure supply chain services.
The Bottom Line
Building a secure supply chain is no longer optional – it’s essential to protecting business continuity, customer trust, and mission‑critical operations. As threats evolve and supply networks grow more complex, organisations must combine strong governance, modern security models, and trusted partners to safeguard every component and dependency.
The organisations that invest in secure supply chain practices today will be the ones best positioned to operate confidently, adapt quickly, and stay resilient in an unpredictable world.
Frequently Asked Questions
What is a Secure Supply Chain?
A secure supply chain is the end‑to‑end assurance that hardware, software, services, data, and third parties are authentic, uncompromised, and resilient – from sourcing and build to delivery, operations, and end‑of‑life. It spans physical, digital, and hybrid (people/process/vendor) controls.
Why is secure supply chain important for businesses today?
Because attackers increasingly target suppliers, software dependencies, and logistics partners, making supply chains one of the most common entry points for cyber and operational disruption.
What are the main risks of an insecure supply chain?
Key risks include compromised software updates, tampered hardware, data breaches through vendors, fraud in transactions, regulatory non‑compliance, and business continuity failures.
How does a secure supply chain differ from traditional cybersecurity?
Traditional cybersecurity protects your own network and apps. Secure supply chain extends that perimeter to vendors, sub‑vendors (Tier‑2+), code dependencies, firmware, logistics, and data flows—treating supplier risk and component integrity as first‑class security concerns.
What are the core components of secure supply chain security.
Core components include supplier risk management, software integrity controls (such as SBOMs), physical chain‑of‑custody, data governance, continuous monitoring, and incident response coordination.
What frameworks or models should we follow to improve supply chain security?
Use a Zero Trust mindset (no implicit trust), pair it with software integrity controls (SBOMs, signed artifacts, hardened CI/CD per SLSA), and enforce risk‑based vendor governance (due diligence, contractual security clauses, continuous monitoring). For hardware, add provenance checks, tamper‑evident logistics, and chain‑of‑custody.
How do organisations manage third-party risk effectively?
Tier suppliers by criticality, collect evidence (certifications/attestations, secure SDLC claims), test incident responsiveness (notification SLAs, joint playbooks), and re‑assess continuously (breach/watchlist monitoring, credential hygiene, token scope reviews).
Is a secure supply chain only relevant for large enterprises?
No. Any organisation that relies on cloud services, software vendors, hardware suppliers, or logistics partners faces supply chain risk, regardless of size.
- Introduction
- Types of Secure Supply Chain
- Why Secure Supply Chain Matters
- Key Challenges to Secure Supply Chain
- Best Practices for Supply Chain Security
- Benefits of Strengthening Supply Chain Security
- Trends Shaping Secure Supply Chain
- Key Considerations and Decision Factors
- How Touchpoint Helps Strengthen Your Secure Supply Chain Efforts
- The Bottom Line
- Frequently Asked Questions


